Send Teams Notification when A User Logs in through RDP
In this short tutorial, I'll show you how to create a simple Powershell script that sends a Microsoft Teams notification whenever someone logs into a computer or server.
There are a number of reasons you might want to setup a login notification like this.
- Auditing login/logoff events
- Monitoring critical servers
- Keeping an eye on highly-sensitive servers (backup server, domain controllers, file share, password vault, etc)
- Time-tracking
Sure, you could always look through Event Viewer to find this info, but a more proactive solution would be to get alerted as soon as the login event happens. Although this script will send a Microsoft Teams channel notification as soon as someone logs in, it wouldn't be that difficult to have it alert via email, SMS, or another chat app like Slack instead. It's a really useful script to track remote computer logins or logoffs.
Generate Teams Webhook
The first thing you'll need to do is add the Incoming Webhook to one of your Office 365 Groups. If you don't want these alerts to go to everyone in a group for testing, I recommend creating a "Notifications Test" Office 365 group and just adding yourself.
Click the 3 dots next to the Team > Connectors > Incoming Webhook > Configure. Here are some steps to generate an incoming webhook if you need them.
Powershell Script to Get Logged in RDP User
The first line of the script will first get the username of the person who remoted into the computer and store it as a variable ($var).
The 2nd line will get the computer name and store it as a variable $comp.
The 3rd line will get today's date and time $date.
If you want a simple, generic message via Microsoft Teams, you could use this:
Invoke-RestMethod -Method post -ContentType 'Application/Json' -Body '{"text":"Someone logged into the backup server!"}' -Uri https://website.webhook.office.com/webhookb2/However, I wanted my message a little more dynamic - I wanted it to show me the date and time, as well as the user who logged in. Unfortunately, we can't use variables in the generic message alert above; if we added $var - we would see $var in the message.
So we use strings like the full script below (blue)
In the $JSONBody variable, this is how we're formatting the message. Feel free to change the text with your own (green text)
In the $parameters section, this is where you'll paste your Teams webhook URL. (orange text)
I purposed left the Summary and Title generic and didn't specify something like "Backup Server Login Notification", simply because I plan on using this on several servers and didn't want to have to customize the message for each server. I'll let the variable in the body tell me the server name.
[String]$var = (Get-ChildItem Env:\USERNAME).Value [String]$comp = hostname [String]$date = Get-Date -DisplayHint Date $JSONBody = [PSCustomObject][Ordered]@{ "@type" = "MessageCard" "@context" = "<http://schema.org/extensions>" "summary" = "Server Logon Alert!" "themeColor" = '0078D7' "title" = "Server Logon Notification." "text" = "$var logged into $comp on $date." } $TeamMessageBody = ConvertTo-Json $JSONBody [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls -bor [Net.SecurityProtocolType]::Tls11 -bor [Net.SecurityProtocolType]::Tls12 $parameters = @{ "URI" = 'https://office.com/webhookURL' "Method" = 'POST' "Body" = $TeamMessageBody "ContentType" = 'application/json' } Invoke-RestMethod @parameters- Open Powershell ISE. Paste in the code above and change out the text (optional) and Webhook URL.
- Save the file to a folder like C:\Scripts\ and save it as
TeamsLogonNotification.ps1. - Then, create a scheduled task that runs when a remote session is connected.
Note: I had to add the below code so the scripts otherwise Teams wouldn't always send the alert:
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls -bor [Net.SecurityProtocolType]::Tls11 -bor [Net.SecurityProtocolType]::Tls12Create Scheduled Task
Open Task Scheduler.
Right-click Task Scheduler Library > Create Task.
General Tab
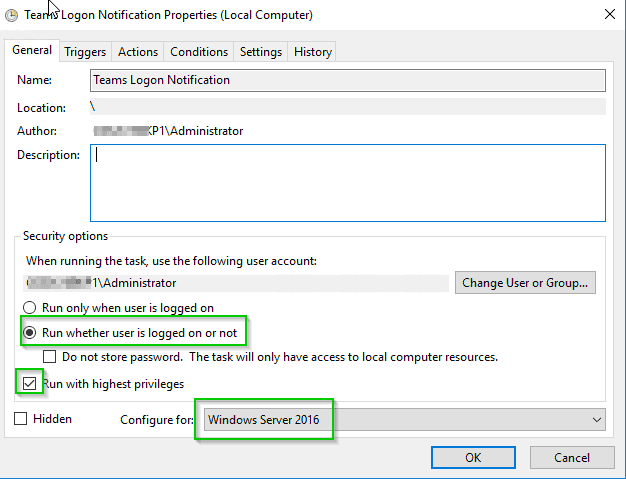
Name: Teams Logon Notification
Set it to run with highest privileges, where whether the user is logged in or not, and configure for your operating system version.
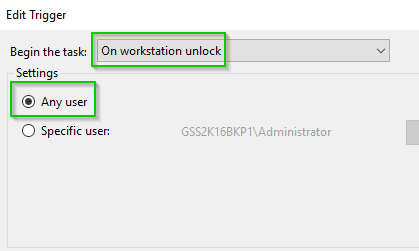
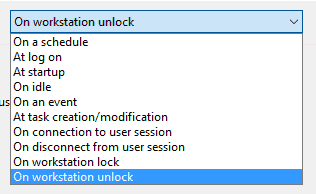
Triggers Tab
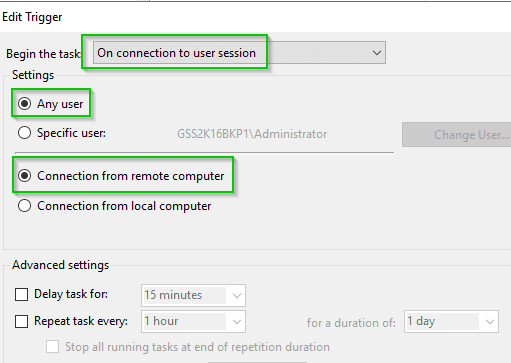
Under Triggers, click New.
- Begin the task: On workstation unlock
- Settings: Any User
I chose the "on workstation unlock" trigger because we have a GPO that locks computers and servers after 15 minutes. If we used another method (such as 'on connection to user session'), then it would also trigger the script if the user logged in from a signed out state, but not if the user logged when their session was just locked.
Actions Tab
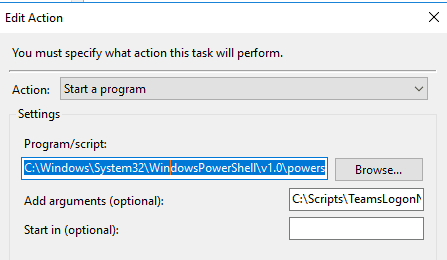
- Action: Start a Program
- Program/Script:
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe - Add Arguments: the path to your TeamsLogonNotification.ps1 file (
C:\Scripts\TeamsLogonNotification.ps1)
That's it! Save the scheduled task and close out of your RDP session or sign out of the server.
Then, RDP to it again.
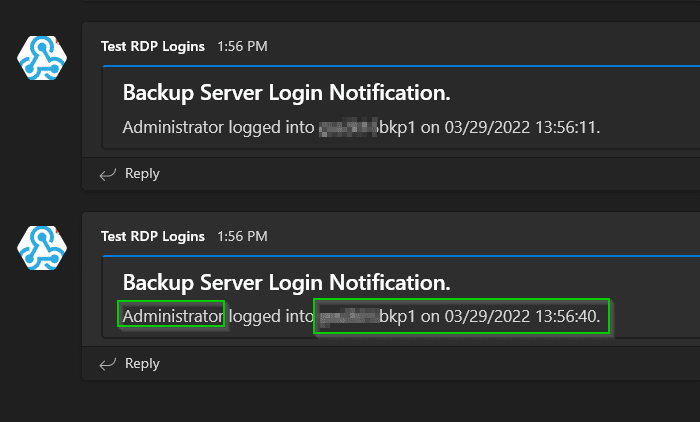
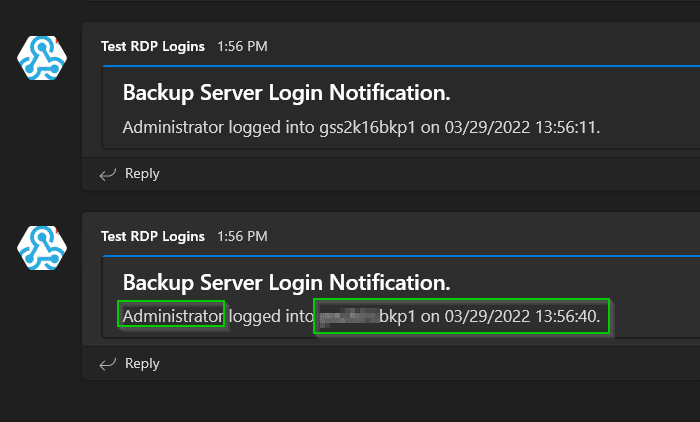
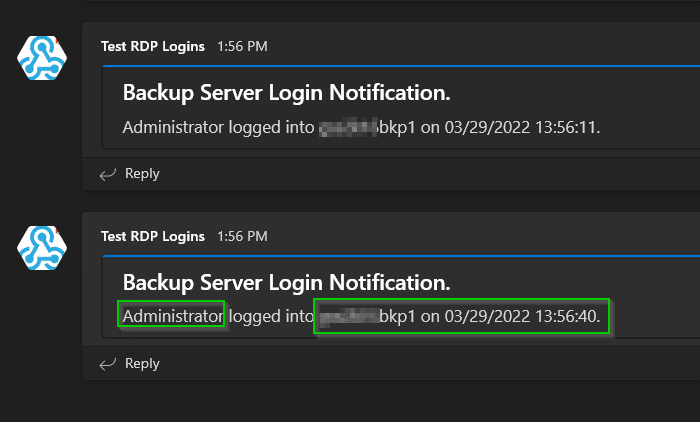
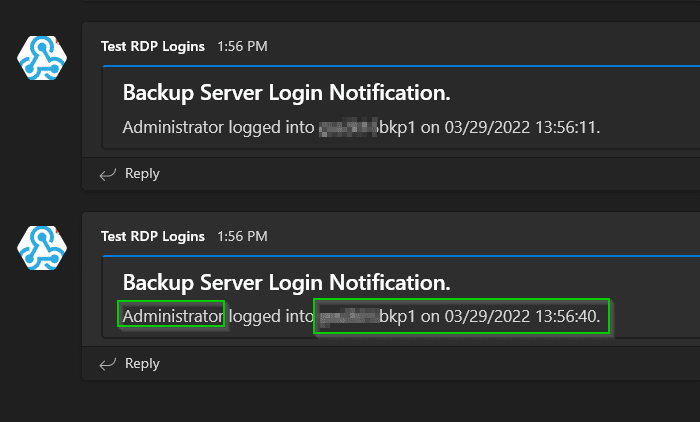
If all goes well, you should see a Microsoft Teams notification that looks like this!
Wrapping Up
This is a handy, simple way to be notified whenever someone logs into a server. Personally I use it for auditing logins to our Veeam backup server and domain controllers. It could also be helpful if you hire a new IT employee and are starting to delegate more privileges and you want to make sure that new hire isn't logging into servers they aren't supposed to yet.