Bitwarden Enterprise Offboarding & Permanently Deleting Accounts
At my company, we are in the process of rolling out Bitwarden Enterprise as our corporate password manager. I've used Bitwarden personally for years, so I'm very excited to implement a tool I use everyday to furhter secure the entire company.
However, one thing that was not mentioned anywhere in the Bitwarden documentation or Bitwarden Offboarding guide was how to delete a Bitwarden account. You can remove a user from the corporation so they won't have any access to shared collections, but that doesn't fully delete a users' Bitwarden account. So, that leaves you with two options
- Logging into the account itself as the end user. This allows you to export the data in case your company may need it.
- Delete account without logging in here: https://vault.bitwarden.com/#/recover-delete This permanently deletes the account; you will not be able to retrieve the data. You will also need access to the employees email account to confirm deletion.
In fact, this quote comes straight from the Bitwarden Offboarding guide:
"When Jane is removed from your Organization, she can continue to use any Bitwarden application to access her Personal Vault, however she will immediately lose access to the Organization Vault, all Collections, and all shared items.
To be honest, this shocked me a little. I didn't realize this until after already getting approval to purchase & implement. I had already spent hours creating training materials and how-to videos in preparation for our big rollout, so this realization was a bit concerning to me.
So, ex-employees that have stored company credentials in their Personal vault (using a company email address) can still be accessed, even after they leave the company? I suppose I can just force delete all accounts, but what if there are critical passwords the company may need?
I knew there had to be a way to fully delete an account but retrieve the data first, so I'm documenting the process for Option 2 above for anyone else who may have the same concerns.
Let's get started!
This guide is tailored to Bitwarden Enterprise admins who have secured their organization with Duo 2FA.
Bitwarden Enterprise: Personal Vault vs. Organization Vault
You may be wondering: What's the difference between a personal Bitwarden vault and an Organization vault?
A personal vault is a password vault accessible only by the employee by logging in with their corporate email address. No one, not even the IT department, can access a user's personal vault.
An organization vault is a corporate vault where Bitwarden admins can create password Collections to be shared among departments or other employees.
I did want to point out that you can completely disable the ability to save passwords to a personal vault, but that gets complicated really quick. You would have to create a Collection in the corporate vault for each user and then add that user to the collection. For smaller organizations, that may be fine, but for my org - we have ~350 users and that would be pretty time-consuming.
For this scenario, my users have personal vaults with a company email and have access to shared Collections because they have accepted the invite to our Bitwarden Organization.
Bitwarden Onboarding Procedure
Whenever you invite a user from the Bitwarden admin portal, here's the basic procedure:
- The IT department sends an invite to the users corporate email address.
- Once the employee creates a Master Password and completes enrollment, the IT department "approves" adding them to the "Organization". (Adding them to an Organization allows admins to apply enterprise policies, such accessing shared password collections and enforcing two-factor authentication)
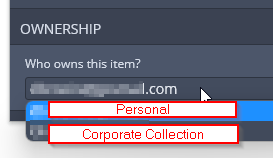
- Whenever employees add a new password to Bitwarden, they have the option to save to their personal corporate vault, or save to the shared collection:
How to Fully Delete A Bitwarden Enterprise Account
Now that you understand a little bit about how the Bitwarden management works, here's the basic procedure to fully deprovision an account and revoke all access. This will permanently delete a Bitwarden account, along with any saved corporate passwords or personal passwords.
I recommend taking an export of the users personal vault and storing it somewhere safe before deletion, just in case. (We also have a non-domain joined PasswordState vault secured by Duo 2FA that only IT can access, so we upload our exports there for safekeeping.)
Note: This does not delete any shared collections the user has created or has access to. Any passwords they have added to a shared collection will remain in the corporate collection.
Here's the basic deletion procedure:
- Disable access to employees email account
- Reset their Master Admin Password.
- Disable/Bypass their Duo account.
- Log into their Bitwarden account.
- Export personal vault / save somewhere secure / delete exported .csv
- Delete their personal Bitwarden account
Step 1: Disable Email Access
First, you'll want to disable the employees email account and/or block the ability to sign in. During the next step, we will be resetting their Master Password.
Resetting a users Master Password will send the employee an email, so we want to make sure they don't see that email and potentially reset it themselves, especially if the employees isn't leaving on their own accord.
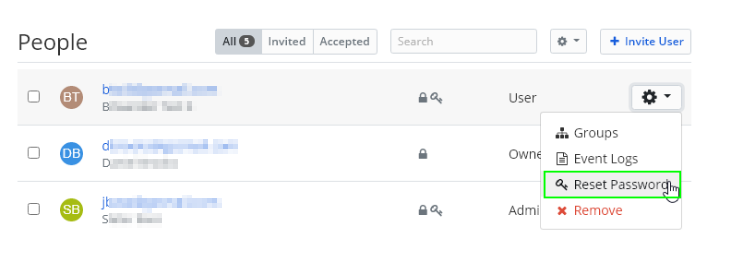
Step 2: Reset their Master Password
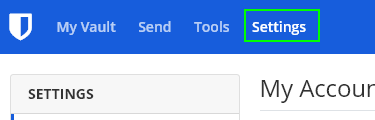
From the Bitwarden admin portal, go to your Organization page. This assumes you've enabled the ability for a user to reset their master password whenever you invited them.
Manage > People. Click the gear > Reset Password.
Take note of the new password you created. Resetting their master password will also sign the user out of all sessions.
Step 3: Disable corporate 2FA
If using Duo with Bitwarden, you can put their user account into "Bypass Mode", which will temporarily not require 2FA when logging into applications.
Go ahead and put their Duo account into Bypass for now.
To be honest, I'm not 100% sure how this would work if you used another form of 2FA, such as Authy or Google Authenticator. You may not be able to continue if using another method.
Step 4: Log into the employees Bitwarden Account
Now that you've reset their password, you can log into their account from an incognito browser at https://vault.bitwarden.com/.
Log in with their email address and newly changed master password. Since Duo has been deactivated, you should be able to log in straight away without 2FA.
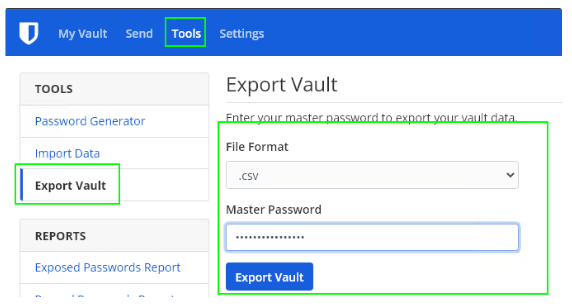
Step 5: (Optional) Export Personal Vault / Save
Once logged into their account, click the Tools tab.
- File format: .csv (there is also an encrypted JSON format)
- Master Password: Enter the newly changed master password
This only exports password from their Personal vault, not passwords in a Shared Collection.
Reminder: Passwords the ex-employee saved to an organization collection are not deleted when their account is deleted.
Once their vault is exported, I recommend storing it somewhere safe, like an on-prem password vault such as PasswordState, printing them out and giving them to HR, or storing them in a IT file share with file-auditing enabled and very tight ACL's.
After exporting and saving somewhere secure, permanently delete the export from your computer (Hold Shift > Right-click > Delete)
Step 6: Delete their Personal Bitwarden Vault
Now that their vault has been backed up in case anyone from the company needs access to a password only they had, you can safely delete their account.
Click the Settings tab > scroll to the very bottom > locate the Danger Zone section.
That's it! You can now fully delete the user account. From your Bitwarden "Organization" screen, the user will notice that the employees' account is nowhere to be found, so you don't need to worry about removing them from there after the account has been deleted.
Wrapping Up
All in all, as long as you warn employees in advance before the rollout that their Bitwarden account will be fully deleted if they ever the company, then this shouldn't be a problem.
Hopefully if you are rolling out Bitwarden Enterprise, you already have a corporate-managed 2FA like Duo instead of something like Google Authenticator, otherwise - you may not be able to fully revoke their account in the event they leave the company.
If you're reading this before before deploying Bitwarden, then you may want to either implement Duo first, or disable the ability to save to a personal vault and create individual Collections for each user.
Anyway, hopefully this guide helped you out a little bit!